Check out this collection of posts where I dive into the fascinating world of attacks on my honeypot and malware. Join me as we explore the wild, and sometimes quirky, side of cybersecurity!
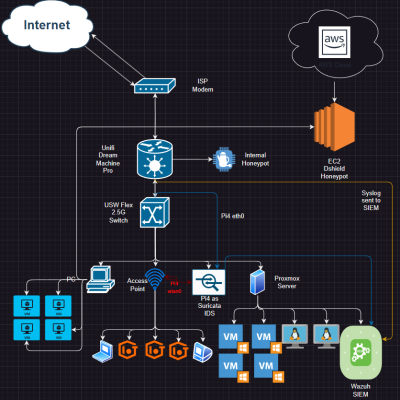
Inside My Ultimate homelab: Mastering IDS, Honeypots, Proxmox, and more.
My setup Over the past year I have acquired various pieces of equipment and computers…
Decoding The Legendary Stuxnet In Memory
Executive Summary Stuxnet is one of the most sophisticated pieces of malware ever discovered, often…
XorDDoS: Anatomy of A Linux Threat
On February 28th, 2024, I observed an attack originating from IP 218[.].92.0.60 that was seen…
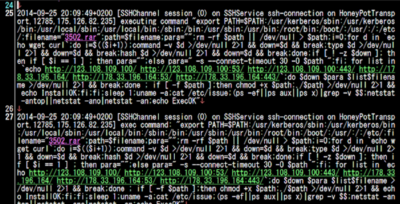
Attack Observation #1
Time & Date of Activity: January 30th, 2024, 00:49:04Z Relevant Logs IP 161.82.233[.]179 was noted…
Metasploitable Part 1: Infiltration & Command Execution
Infiltrate Metasploitable In this post I am going to be diving into some web application…
SQL Injection
What is a SQL Injection attack? To understand what a SQL injection attack is you…